The theme of the last three blogs was “look behind the curtain” in order to tell the fraud story. Upon reflection, maybe I did not tell the entire fraud story. Maybe, I did not look behind the right curtain. So, this month, we are going to look behind a different curtain.
Fraud Auditing, Detection, and Prevention Blog
An Analysis of Modern Internal Control Structures and Their Efficacy
Aug 21, 2024 8:25:58 PM / by Leonard W. Vona posted in Fraud Auditing ...
What’s Behind the Internal Control Curtain? Is it a Fraud Story?
Jul 22, 2024 2:49:59 PM / by Leonard W. Vona posted in Fraud Schemes ...
This month, we're pulling back the curtain again to take a look at a look at what could be going on even when everything seems to be fine on the surface. We'll consider what can happen despite the appearance of effective internal controls and how to uncover it.
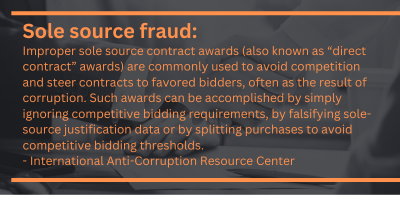
A Look Behind the Curtain: Sorting out Sole Source Vendor Fraud
Jun 19, 2024 2:31:30 PM / by Leonard W. Vona ...
This month, we're showing how to "look behind the curtain" to uncover fraud using a sole-source contract as an example. This is when a contract is intentionally written to go to a particular vendor with ill intent.
Fraud Audit Insights: Revealing The Fraud Story
May 20, 2024 2:05:54 PM / by Leonard W. Vona posted in Fraud Schemes, Fraud Auditing, ...
My last series of blogs discussed strategies for detecting shell companies. I know they work because I have refined the strategies throughout my career. Now we will discuss what causes those strategies to fail.
What are the inhibitors to the successful use of artificial intelligence in fraud detection? Humans.
Calling for a Fight Against Human Trafficking
Apr 23, 2024 1:44:48 PM / by Leonard W. Vona ...
This month's blog is dedicated to making you aware of the scourge on society. Slavery. We now call it human trafficking. The United Nations explains human trafficking as follows:
Anatomy of a Real-life Shell Company Pass-Through Scheme
Mar 20, 2024 11:39:15 AM / by Leonard W. Vona posted in Fraud Data Analytics, Fraud Risk Identification, ...
This story is about a passthrough scheme. It is my opinion that most large companies have one of more pass-through schemes occurring. What makes it difficult to detect or prevent these schemes is that the scheme will comply with all of your controls. Your company has received the goods or services. Therefore, your ability to detect these schemes is predicated on your understanding of how these schemes occur and what they look like.
Mastering Shell Company Detection: Steps for Fraud Auditors (Part 8)
Feb 13, 2024 4:37:48 PM / by Leonard W. Vona ...
In our next two blogs concerning shell companies, I will highlight real-life shell company schemes detected by our firm using the fraud audit methodology discussed in our blogs. Remember, all these schemes were found in large publicly traded companies using the fraud audit methodology discussed in the last seven blogs. I have changed the names of the companies to respect the confidentiality of our clients. It is important to note that there were no allegations, no whistleblowers, and no leads.
Mastering Shell Company Detection: The Written Report (Part 7)
Jan 18, 2024 7:29:00 AM / by Leonard W. Vona ...
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then delve into a demonstration of the fraud audit process.
Mastering Shell Company Detection: Is Their Credible Evidence to Perform a Forensic Exam?
Dec 12, 2023 9:49:22 AM / by Leonard W. Vona posted in Fraud Auditing, Fraud Based Approach, ...
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then delve into a demonstration of the fraud audit process.
Mastering Shell Company Detection: Practical Steps for Fraud Auditors: Part 5
Nov 15, 2023 12:14:12 PM / by Leonard W. Vona posted in Fraud Risk Statements, Fraud Schemes, ...
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then delve into a demonstration of the fraud audit process.