In one sense, there is nothing new when it comes to misstatement of revenue in financial statements. With a little effort, you can find real-life examples of these schemes in both publicly traded companies and privately held companies. How the scheme is perpetrated may differ by industry or by company. How the scheme is concealed may differ by industry or by company. So, how can auditors uncover these schemes?
Fraud Auditing, Detection, and Prevention Blog
Revenue Fraud Schemes: Do You Really Understand Them?
Apr 21, 2026 7:57:50 AM / by Leonard W. Vona posted in Fraud Risk Statements, Fraud Schemes, ...
Gaining a Deeper Understanding of Fraud Schemes
Mar 13, 2025 4:00:00 PM / by Leonard W. Vona posted in Fraud Schemes, Fraud Auditing, ...
Before I start, let me explain that in this blog I will not provide any answers to the phrase “Deeper Understanding of Fraud Schemes.” Rather, I will only raise questions regarding the phrase. To be honest, If I was a CAE, I am not sure what the profession wants me to do.
With that said, I praise the profession in recognizing the importance of gaining a deeper understanding of fraud schemes facing our companies. Maybe, I am talking out of both sides of my mouth. Remember, my blogs are designed to make you think.
So, think about this: Fraud is not predictable as to when it will occur but is fairly straight forward as to how it will occur.
Proactive Approach to Fraud Detection: A New State of Mind
Feb 24, 2025 7:19:20 PM / by Leonard W. Vona posted in Fraud Auditing, Fraud Detection, ...
Many years ago, the IT auditor was created. In fact, I was an IT auditor in 1979. For the last 40 years, however, I have been a fraud auditor. Unfortunately, unlike IT, the profession does not recognize the title of fraud auditor.
In my opinion, it is time for the title of Fraud Auditor to be created and recognized by the profession. Auditors are not born with fraud risk or fraud audit knowledge or fraud skills. I suspect that college courses are not designed to provide this knowledge. If the profession is serious about a “more proactive approach to fraud detection” it is time to recognize that this will require auditors to develop and gain a new set of skills. I recommend that every audit department invests in human fraud risk intelligence.
Is Fraud Auditing About Mitigating or Managing Risk?
Jan 18, 2025 8:27:17 AM / by Leonard W. Vona posted in Fraud Risk Statements, Fraud Auditing, ...
Current audit standards call for us to use a mitigation standard when it comes to audits This means that unless you want to be an outlaw, your assessment will end with mitigate. However, the question I want you to ask yourself is, right now do we have enough information to properly assess the mitigate question?
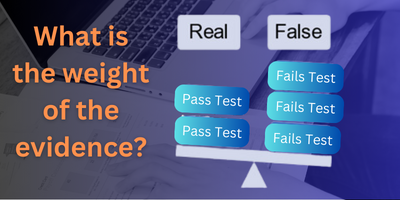
Looking Behind a New Curtain to Improve Fraud Risk Assessment
Oct 18, 2024 8:15:00 AM / by Leonard W. Vona posted in Fraud Auditing, Fraud Detection, ...
This month I will present at a conference a new approach to fraud risk assessment. It is the cumulation of my 40 years of experience in building the fraud audit model.
Mastering Shell Company Detection: Is Their Credible Evidence to Perform a Forensic Exam?
Dec 12, 2023 9:49:22 AM / by Leonard W. Vona posted in Fraud Auditing, Fraud Based Approach, ...
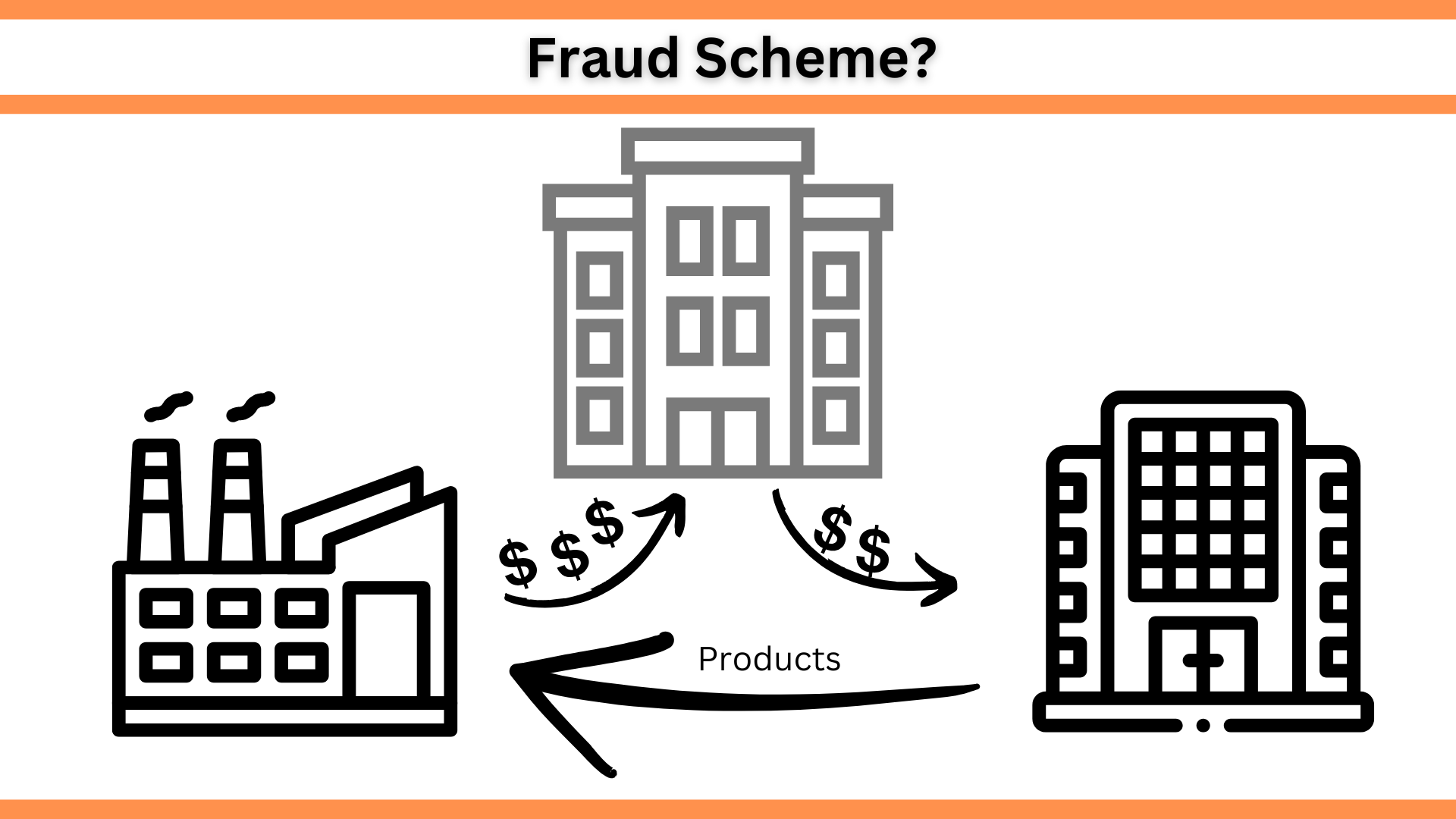
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then delve into a demonstration of the fraud audit process.
Mastering Shell Company Detection: Practical Steps for Fraud Auditors: Part 4
Oct 16, 2023 9:18:00 PM / by Leonard W. Vona posted in Fraud Auditing, Fraud Based Approach, ...
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then delve into a demonstration of the fraud audit process.
Mastering Shell Company Detection: Practical Steps for Fraud Auditors Part 3
Sep 16, 2023 7:30:00 AM / by Leonard W. Vona posted in Fraud Auditing, Fraud Based Approach, ...
In this series of blogs, we are looking at the practice of using a fraud audit to detect shell company schemes occurring in an accounts payable file. Because the practice of effective fraud auditing is grounded in knowledge, we will start with a knowledge section and then demonstrate the fraud audit process.
Mastering Shell Company Detection: Practical Steps for Auditors Part 2
Aug 14, 2023 5:32:05 PM / by Leonard W. Vona posted in Fraud Risk Statements, Fraud Auditing, ...
In this series of blogs, we are discussing how auditors can detect shell company schemes that are occurring in their accounts payable files. Because the practice of effective fraud auditing is grounded in knowledge, each blog will have a knowledge section as well as a practical audit section. (This blog will not discuss how organized crime groups use shell companies to perpetrate criminal activities.)
Using Fraud Auditing to Detect Shell Company Fraud Schemes
Jul 14, 2023 8:20:42 AM / by Leonard W. Vona posted in Fraud Auditing, Concealment Strategies, ...
Using Fraud Auditing to Detect Shell Company Fraud Schemes
The last two blogs were an esoteric discussion on fraud auditing using either a principal-based approach or a rule-based approach. With this blog, we'll launch into the practical use of fraud auditing. By way of example, we will look at how to detect shell company fraud schemes perpetrated against your company. Remember, our goal is to make audit the number one reason for fraud detection.